THM – Simple CTF
Tonight, I decided to go into a CTF box. I’ve been watching tons of CTF videos by John Hammond and The Cyber Mentor, so it was a logical step in trying to pwn a new box on Try Hack Me.
The tutorial was rather vague. I wasn’t sure why it was asking about port 1000 in since NMAP was only showing other ports. For that question of how many services were running on port 1000, I simply took a guess and got it right.
To start owning the box, I did the standard NMAP and Directory scanning. The Gobuster results were fairly quick, and showed a directory that reveiled a service being run called CMS Made Simple. It was pretty easy to find an exploit… I googled “exploit CMS made simple.” This reveiled the CVE number, and a python script.
The python script (after making it executable) had some errors. It turns out that I didn’t have some required imports for the script. After a pip install, it actually ran.
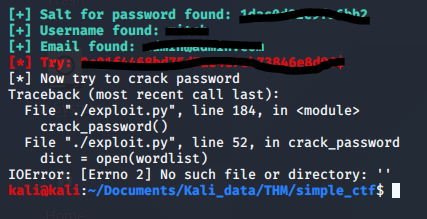
I got some errors, but obtained enough information to bring it over to hashcat. For some reason, it wasn’t checking out my rockyou.txt file to crack the password.
Once I had the user name, and the password, it was as easy as using that SSH service that I discovered through NMAP using a different (non-standard) port. using the ‘-P’ flag on SSH, it allowed me to log into the box using the account that I found. From there, I could do a list of the commands that I could run as sudo. This was done with a ‘sudo -l’ command which is pretty common for listing the sudo commands that a user can run.
The command that was found was extremely easy to use, and had a way to get a shell with root. After that, I simply read the flag from the /root/ folder and completed the challenge.
