THM – Mr Robot
NOTE: This is not a tutorial on the Mr Robot machine hosted by Try Hack Me. It is simply an overview of the strategy used to defeat the box, and a reference for that strategy.
The target machine was a simple server hosting a webpage. Other than the web ports, and SSH, there was nothing else to exploit. I ran across the wordpress construct right after I did a dirbuster search on the box. As soon as I saw ‘wp-content’ in the list, I felt pretty comfortable about the organization of the folders. Knowing the wordpress structure through years of experience allowed me to notice if anything of importance stood out. It also allowed me to play with a tool with which I don’t have much experience… wpscan.
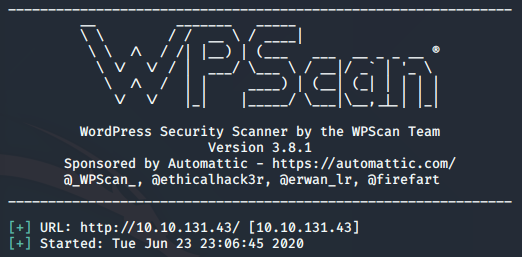
It’s not uncommon to run multiple scans at once and look at results in real time as they present themselves. I mentioned the dirbuster results, but also ran wpscan as soon as wordpress was discovered. I didn’t have many results on that tool other than some suggestions for referenced attacks using meterpreter (wasn’t interested in that here), and some information about versions.