Bastard on HTB – Retired
BASTARD – HTB
RETIRED
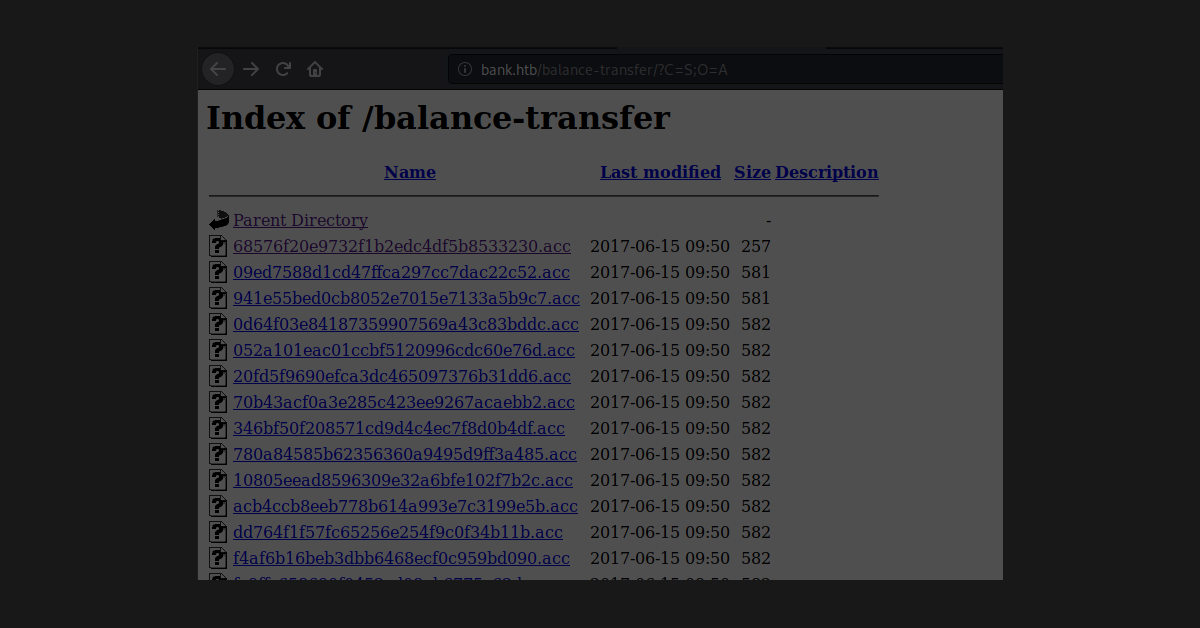
NMAP
Nmap 7.91 scan initiated Fri Feb 12 23:36:02 2021 as: nmap -A -p- -T4 -oG nmap.init 10.129.29.109
Host: 10.129.29.109 () Status: Up
Host: 10.129.29.109 ()
Ports:
80/open/tcp//http//Microsoft IIS httpd 7.5/,
135/open/tcp//msrpc//Microsoft Windows RPC/,
49154/open/tcp//msrpc//Microsoft Windows RPC/
Ignored State: filtered (65532)
Nmap done at Fri Feb 12 23:38:42 2021 — 1 IP address (1 host up) scanned in 160.81 seconds